The best way to protect yourself in the cyber world is to know how to carry out attacks. If you want to venture into the DDoS attack method, below are some of the top DDoS attack tools you can use in the market.
You will agree with me that it can be frustrating to go to a website to accomplish a productive task but be unable to proceed due to Internet congestion.
Sometimes the website may be getting a lot of traffic for genuine reasons, and other times it may be the result of malicious hacker activities. DoS attacks are the term used to describe these deliberate web server attacks.
A cyber-attack known as a “Denial of Service,” or “DOS,” prevents authorized users from using a resource such as a website, email, network, etc. However, attacks known as distributed denial of service (DDoS) have grown to be a danger to existing networks.
As such, “Distributed Denial of Service” attacks use a collection of infected workstations to prevent normal users from accessing resources. By flooding the computer network with data packets, all of these compromised computers attack the same victim. An application layer attack, a protocol attack, or a volume-based attack are all examples of DDoS attacks.
A hacker might receive a prison sentence because it is illegal. To correctly carry out these cyber-DDoS attacks, however, a number of actions must be taken. Nevertheless, both open source (free) and commercial (paid) DDoS attack tools are included in the list below.
1. LOIC
A well-known DoS tool that has become legendary among hackers is LOIC. The Low Orbit Ion Canon, or LOIC for short, was initially created in C# by a company named Praetox Technologies.
Nevertheless, it was subsequently placed in the public domain. This attack tool tends to be extremely helpful in DDOS attacks that take advantage of enormous volumes.
It directs computer networks’ connections to particular server architectures. Since no computer can typically send requests strong enough to consume all available server bandwidth, they cause computer networks to send pointless packets to the preselected servers. This program requests data from the server via HTTP, TCP, and UDP.
Features:
- The DDoS attack tool LOIC is free.
- Users can conduct stress tests because to it.
- It does not conceal an IP address even when the proxy server is unavailable.
- It can be used to identify DDoS applications that hackers may employ.
2. HULK (HTTP Unbearable Load King)
Another effective DOS attack tool is HULK, which creates a distinct request for each one it sends in order to mask web server activity. It is officially referred to as HTTP Unbearable Load King (HULK) and is one of the free DDoS attack tools that is specifically employed.
It is simple for attacks to overwhelm servers with many of these seemingly legitimate requests, currently where transfer protocols are the norm for computer-server communication. HULK operates in just that way. The Python-based HULK program can be used on any operating system that has Python installed. Linux, Windows, and Mac are a few of these OSs. Switches, routers, and firewalls may all be tested using the HULK tool.
Features:
- This technology allows us to create distinctive network traffic.
- The cache server can be avoided by HULK.
- This tool can be used by users for study.
3. PYLORIS
PyLoris is a powerful tool for performing stealthy DDoS attacks. It is yet another piece of network vulnerability testing software that analyzes network vulnerabilities using a distributed denial-of-service (DDoS) attack.
PyLoris has a user-friendly Graphics User Interface (GUI) that affords ease of use. It assists you in controlling poorly handled concurrent connections and managing DDoS attacks online. With the aid of SOCKS proxies and SSL connections, this program may launch a DoS attack against a server.
Among the protocols it can target are HTTP, IMAP, FTP, SMTP, and Telnet. It has python dependency, but installation also can be difficult. It can make attacks on various protocols, though.
Features:
- Python can be used to run PyLoris.
- It has a user-friendly GUI (Graphic User Interface).
- You can attack utilizing HTTP request headers thanks to this tool.
- Linux, Mac OS, and Windows are all supported by this utility.
- The newest codebase is utilized (a codebase is a collection of source code used to build a particular software system).
- With a cap of 50 threads and a total of 10 connections, it has a more sophisticated alternative.
4. TORS HAMMER

Attacks inside the Tor network are possible using the Tor hammer. In order to anonymize the attack and restrict the available mitigation techniques, the Tor Hammer was created to operate via the Tor network. This online DDoS tool can be used to attack web servers and web applications.
The OSI Model’s level 7 describes its operation. The utility opens numerous dead connections, which causes the application to hang because it is unable to send a response. However, it is designed specifically for covert attacks rather than a crushing motion like the genuine Thor hammer. The tool’s design makes use of anonymity to get through firewalls and security mitigations.
Features:
- It holds HTTP POST requests and connections for 1000 to 30000.
- It enables us to create rich text markup using Markdown (a plain text formatting syntax tool).
- The Tor’s Hammer automatically converts the URL into links.
- With the help of this tool, we can quickly link other artifacts in our project.
- Tor’s Hammer uses web server resources by creating several network connections.
5. DAVOSET
With the use of the software DAVOSET, DDoS assaults can be started by abusing any feature of a website. By abusing the functionality of any website, users of this software can start DDoS attacks. The DAVOSET command-line software makes it simple to carry out widespread denial-of-service attacks.
Website-to-website communication typically makes use of the structures employed in this context. It uses the shortcomings of XML external entities, among other structures. DAVOSET is an open-source DDoS attack tool that is easy to use. Users can use the command line to attack the sites using a list of zombie servers as well as remove non-working services from the lists of zombie servers.
Features:
- One of the DDoS tools that support cookies is this one.
- The command-line interface for this DDoS attack on open-source software is available.
- Additionally, DAVOSET can help us counter attacks that make use of XML external entities (attack against an app that parses XML input).
6. GOLDEN EYE
On GitHub, you may download GoldenEye, a free and open-source program. By making an HTTP request to the server, the program launches a DDoS assault.
To prevent socket connection bursting, it uses a KeepAlive message in conjunction with cache-control parameters. .NET Core was used to create the framework for this utility. We can use the numerous base classes and extensions provided by this tool in our everyday work.
Servers are the only audience for GoldenEye. Although it was created as a test tool for servers, hackers have found ways to exploit it and can now use it in sophisticated DDoS attacks.
Features:
- It is one of the Python-written DDoS tools that are simple to use.
- GoldenEye is a free-to-use open-source tool that may be downloaded from GitHub.
- In order to launch a denial-of-service attack, GoldenEye can generate a significant volume of botnet traffic.
- GoldenEye makes use of entirely legal HTTP.
- This tool allows us to launch DDoS assaults on any web server.
- GoldenEye bombards the target with requests, which causes a lot of traffic from botnets.
7. RUDY
Are You Dead Yet? is the abbreviation for RUDY. It is a free DDoS attack tool that makes it simple for people to launch an online DDoS attack. RUDY is a popular low and slow attack tool by limiting the number of web server sessions, it targets cloud services.
RUDY is utilized in conjunction with additional tools. The first step is to find servers with embedded web forms. With RUDY, you may launch HTTP DDoS attacks by submitting long-form fields. When these servers are identified, and the forms are noted, the RUDY attack tool is used to issue HTTP requests with extraordinarily large content.
Features:
- This is a simple and easy tool.
- It automatically browses the target DDoS website and detects embedded web forms.
- RUDY enables you to conduct HTTP DDoS attacks using long-form field submissions.
- This tool provides an interactive console menu.
- This DDoS free attack tool automatically identifies form fields for data submission.
8. SLOWLORIS
SlowLoris is undoubtedly one of the best tools for DDoS attacks. Slowloris has proven to be quite effective in tests against well-known web server softwares, including Apache.
It operates by opening as many connections to the targeted web server as it can and maintaining them open for as long as it can. Thanks to its simple yet elegant design, the attack consumes extremely little bandwidth and solely impacts the web server on the target host, having almost no negative side effects on other services or ports.
Attackers can also connect to the victim server and keep those connections open for however long is required by using the SlowLoris program.
Features:
- Slowloris makes use of completely legal HTTP traffic.
- This tool allows us to launch DDoS assaults on any web server.
- We can get this tool for free from GitHub because it is open source.
- In order to launch a denial-of-service attack, Slowloris can generate a significant volume of botnet traffic.
- By bombarding the target with requests, Slowloris creates a botnet with high traffic.
9. DDOSIM (DDoS Simulator)

This program is primarily used to simulate application layer DDoS attacks against specific hosts. To launch layer 7 attacks against these servers, this tool generates several fictitious hosts.
Based on how the server security mechanism handled this assault, its strength is assessed. The utility is built in C++ and performs best on LINUX, despite being modified to work on other operating systems. It employs many attack strategies to demonstrate the variety of approaches and the breadth of a hacker’s cognitive process.
DOSIM mimics several zombie hosts (with random IP addresses). Full TCP connections are established to the destination server. After establishing the connection, DDOSIM begins speaking with the listening program.
Features:
- This DDoS test shows whether the server can withstand attacks that are tailored to a particular application.
- You can establish complete TCP connections to the target server thanks to it.
- DDoSIM offers many ways to launch a network attack.
- Any network port can experience a TCP connection flood.
10. HOIC

The widely used and cost-free HOIC DDoS attack tool is accessible on Linux, Windows, and Linux platforms. In addition to being able to send different kinds of packets, HOICs have a higher rate of request generation than LOICs.
Using HTTP POST and HTTP GET requests, HOIC may carry out DDoS assaults. As many as 250 garbage packets per second can be produced by HOICs and sent as requests to servers.
This tool’s attacks do not produce greater bulk. As the sophistication of those attacks rises, detection becomes more difficult. Booster scripts that are already included assist attackers in escaping detection. Many HOIC users utilize Swedish proxies in addition to booster scripts to conceal their location.
Features:
- High-speed HTTP Flood with multiple threads
- Up to 256 DDoS websites may be attacked simultaneously.
- You can measure the output with the aid of the counter it has.
- This DDoS-resistant program is portable to Linux and Mac OS.
- The number of threads used in the current attack is up to you.
- Users can control attacks using the tool’s low, medium, and high levels.
11. PRTG
As a tool that has been around since 1997, PRTG (Paessler Route Traffic Grapher) does not participate in attacks directly. However, the way it operates might be helpful in DDOS attack mitigation.
It is primarily used as a stats tool to monitor server traffic and the amount of bandwidth utilized and to provide alerts when any irregularities in these activities are discovered. It is renowned for having highly developed infrastructure management abilities.
Using technologies like SNMP, WMI, Sniffing, REST APIS, SQL, and others, the program keeps track of IT infrastructure. It also works well against volume-based denial of service attacks and has an intuitive UI.
Features:
- By pinging predetermined IP ranges, PRTG may inspect network segments.
- It assists consumers in producing web pages with the most recent monitoring data in the preferred layout.
- Simple and adaptable alerting.
- A variety of user interfaces
- Users are notified when it detects warnings or anomalous network measurements.
12. OWASP DDOS HTTP POST
Open Web Application Security Project is what OWASP stands for. With the use of this tool, users can check how resilient their online application’s security is against common DDOS attacks.
Depending on who uses it, it is incredibly successful both as an attack simulator and in real attacks. Additionally, the easiest technique to test your system for application-layer threats is with OWASP HTTP Post.
As a result, network and transport layer attacks are not possible using it. According to the author, these tools are easier to detect. The defect of the HTTP GET DDOS is that it does not work on IIS web servers or web servers with timeout limits for HTTP headers.
Features:
- Commercial use is absolutely free.
- Users are able to carry out denial-of-service attacks from a single machine.
- The results can be shared by users in accordance with the license it offers.
- It enables users to share and convey the tool to other people.
- It assists users in determining the server’s capacity.
- With the help of this program, you can test for application layer threats.
13. Sucuri
Sucuri is a free DDoS program that safeguards you from potential attacks. With the help of the Web Application Firewall, it provides comprehensive virus and hacker security for your website (WAF). The WAF blocks most of the malicious activity and keeps hackers out of your system. Sucuri also protects you against password-cracking brute-force assaults.
Important login information for your website won’t be compromised or disclosed this way. Sucuri’s approach to mitigating network-based attacks includes investing in resources across all PoP locations. It’s built on an Anycast network that allows the distribution of all inbound traffic across the network and explicitly blocks all non-HTTP/HTTPS-based traffic.
Features:
- It only needs web server credentials and a DNS update, making setup simple.
- They stop DDoS attacks at levels 3, 4, and 7.
- They offer a Protect Page Feature that you can activate by adding passwords, CAPTCHA, 2FA, and other security measures to specific important websites.
- It protects against malware and hacks using a Web Application Firewall (WAF).
- They continually oversee all server policies and patch upgrades that safeguard your website.
14. Hyenae

Hyenae (Linux app) is an attack simulation program that includes a clusterable remote daemon, an interactive attack assistant, and the ability to simulate various MITM, DoS, and DDoS assault situations. It is well known for being extremely adaptable and universal.
It might be used to carry out various DDOS attacks in a controlled setting. It is frequently the best tool for performing PEN testing because of this. With smart wildcard-based address randomization and a highly customizable packet generation control, Hyenae also comes with a remote daemon for setting up distributed attack networks. It is a highly flexible and platform-independent network packet generator.
Features:
- ARP-Cache poisoning and ARP-Request flooding.
- PPPoE session flooding and blind session termination
- ICMP-based TCP connection reset, ICMP-based Smurf attack, and ICMP-based Echo flooding.
- TCP-SYN flooding, TCP-Land attack, Blind TCP-Connection reset, and TCP-Land attack.
- UDP flooding.
- Active hijacking of a Cisco HSRP router.
- Smart randomization using wildcards.
- Packet address configuration based on patterns.
- Support for HyenaeFE QT-Frontend.
15. Hping
An effective DDoS attack tool is Hping. It is used to transmit packets across TCP/IP, UDP, ICMP, and SYN/ACK and display target responses, much like the ping software does for ICMP responses. Even a three-way server network response attack can be carried out successfully using it.
It may practically transmit any kind of protocol packet to the desired servers. However, it is particularly renowned for displaying how the targets react in an attack scenario. indicating that it is a useful DDoS simulation tool as well.
Hping is no longer being actively developed, though. Users occasionally propose changes, which are then included in the main source tree. The Hping Github repository is the development headquarters.
Features:
- Advanced performance testing of networks.
- Superior port scanning.
- Implement a three-way server network response attack.
16. XOIC
Another excellent DDoS attack tool is XOIC. It is yet another program for Windows that can launch DoS/DDoS attacks without error. The creator of XOIC asserts that it is more potent than the open-source, multi-platform LOIC.
In the attack mode, XOIC features an additional ICMP flood. XOIC also contains a Test Mode, which can be used to evaluate the effectiveness of the attack launching host, even though both attack types are traffic related.
However, XOIC can be considered as an advantage for hitting these targets if you’re working with tiny, conventional websites. There are three different assault options. The default mode, the typical DOS attack mode, and the TCP/HTTP/UDP/ICMP-based DoS attack mode.
Features:
- Simple to use GUI
- It offers three different attack options.
- The TCP/HTTP/UDP/ICMP normal DoS attack mode
- Test Mode will show how long it takes your computer to process 10,000 requests.
- TCP/HTTP/UDP/ICMP message-based denial-of-service attack
17. THC-SSL-DOS
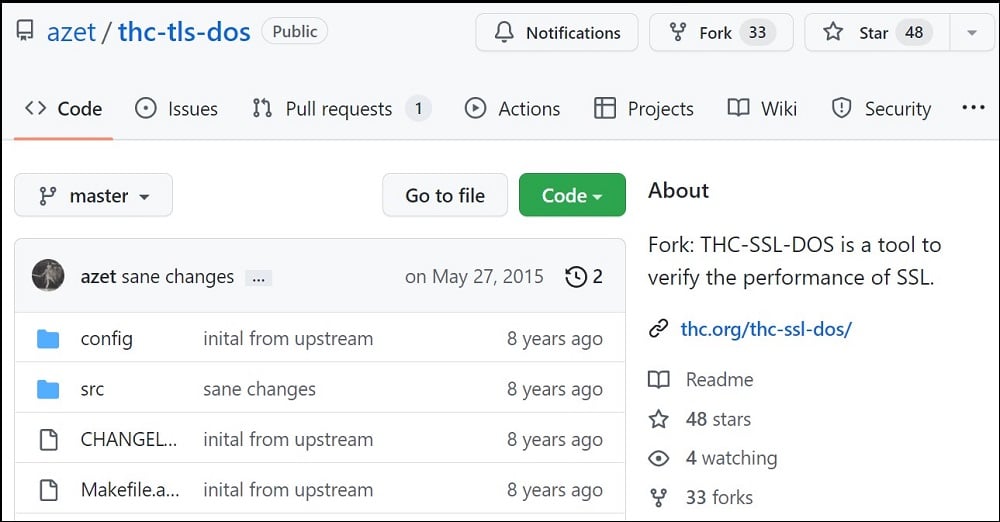
The Hacker’s Choice (THC), a hacking group, created the THC-SSL DOS as a proof of concept to persuade vendors to fix a critical SSL vulnerability. By closing every SSL connection, it causes the server to lag.
It is possible to use just one machine. It operates by starting a conventional SSL handshake and then asking for the renegotiation of the encryption key right away. This resource-intensive renegotiation request is repeated until all server resources have been used up.
This asymmetric trait is taken advantage of by THC-SSL-DOS, which overloads the server and takes it offline. A single TCP connection is used in this attack to launch thousands of renegotiations by further exploiting the SSL secure renegotiation feature.
Features:
- SSL secure Renegotiation
18. APACHE BENCHMARK TOOL
A server benchmark is provided by the Apache benchmark tool (particularly HTTP servers). It is possible to determine the speed of a website’s server by using Apache Bench (ab), a well-liked HTTP load testing and performance benchmarking tool. On the other hand, it is utilized to track web server statistics in real-time. As a result, it is simple to modify for widespread attacks coming from a single source. After running the application for one minute, the user-friendly interface produces results. The Apache web server automatically installs Apache Bench (AB), although the user can also install it individually as an Apache tool. ASP.NET Core APIs can also be used with Apache Bench.
Features:
- It can be used to track the statistics of your web server instantly.
- It can be utilized to carry out load tests.
- Its user interface is simple to use.
- It is compatible with Asp.NET Core APIs.
FAQs
Q. Are DDoS Attack Tools Legal?
DDoS attacks can be disastrous for a business since they prevent current and potential clients from accessing their website. However, a DDoS assault is illegal and subject to legal penalties. On the other hand, DDoS attack tools are dependent. These tools were created with the sole purpose of monitoring, testing, and blocking DDoS attacks.
DDoS attack tests are actual, controlled attacks that help you find vulnerabilities in your system and develop a strategy to safeguard your business. However, there are several more DDoS tools that can be harmful in the hands of a user with malicious intentions.
Q. Can DDoS Attack Tools be Used to Conduct an Actual DDoS Attack?
Yes, they can be utilized to carry out a server hack to bring down reliable web servers. However, bear in mind that these DDoS attack tools were not originally created to be used to cause an attack.
Many of them are created for the purpose of simulating cyber-attacks so that people can learn how cyber-DDoS operations work rather than for actual illegitimate attacks. The tool can cause havoc in the hands of a malicious user.
Q. What is the Best DDoS Attack Tool?
The topic of choosing the best tool is subjective. Depending on the functionality you’re interested in. Many DDoS attack solutions are available to speed up and automate such cyberattacks. SLOWLORIS uses HTTP headers, whereas DDoSIM and Tor’s Hammer work in the seventh layer of the OSI architecture.
The malicious traffic is dispersed by HOIC and LOIC via booster codes, making it challenging to identify an attack. HULK and Golden Eye were first developed for testing but are now utilized for evil purposes as well. Given the abundance of DDoS attack tools available, it’s critical to confirm that the tool’s features meet your needs.
Conclusion
To prevent attacks on the security of your framework, it is advantageous if you are a cyber-security specialist that you are as familiar with these technologies as you can be. Additionally, a number of DDoS attack tools are available to speed up and automate these cyberattacks.
There are various DDoS attack tools available, and some of them are harmful and useful for running simulations. We discussed a few pertinent ones and their roles in this article. If you’re seeking for a solid and dependable DDoS attack tool, you should start with them.

